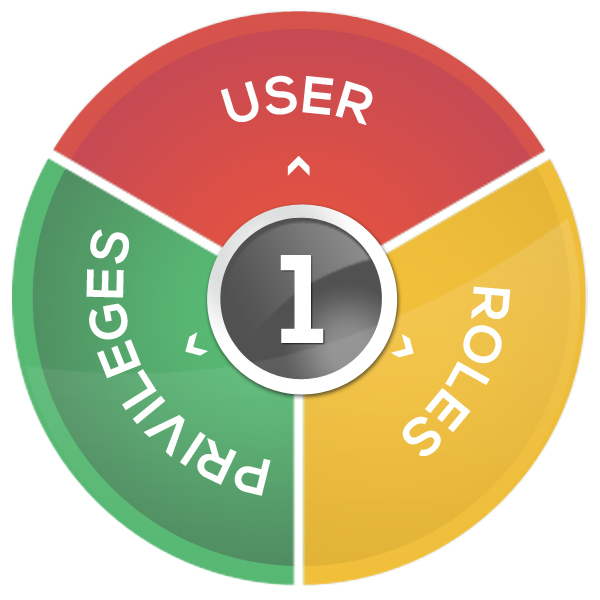
Defining Roles: The Top-Down Process in Practice
Our path to well-defined roles begins with the system owner who evaluates the applications and which users should have access. When he determines that a group does not belong, for example, the accounting folks should not be on a particular application or system, he removes them…All of them. This first pass eliminates users who should […]
Defining Roles: The Top-Down Process in Practice Read More »