Mastering Identity Management: Is HR Creating a Hostile Work Environment?
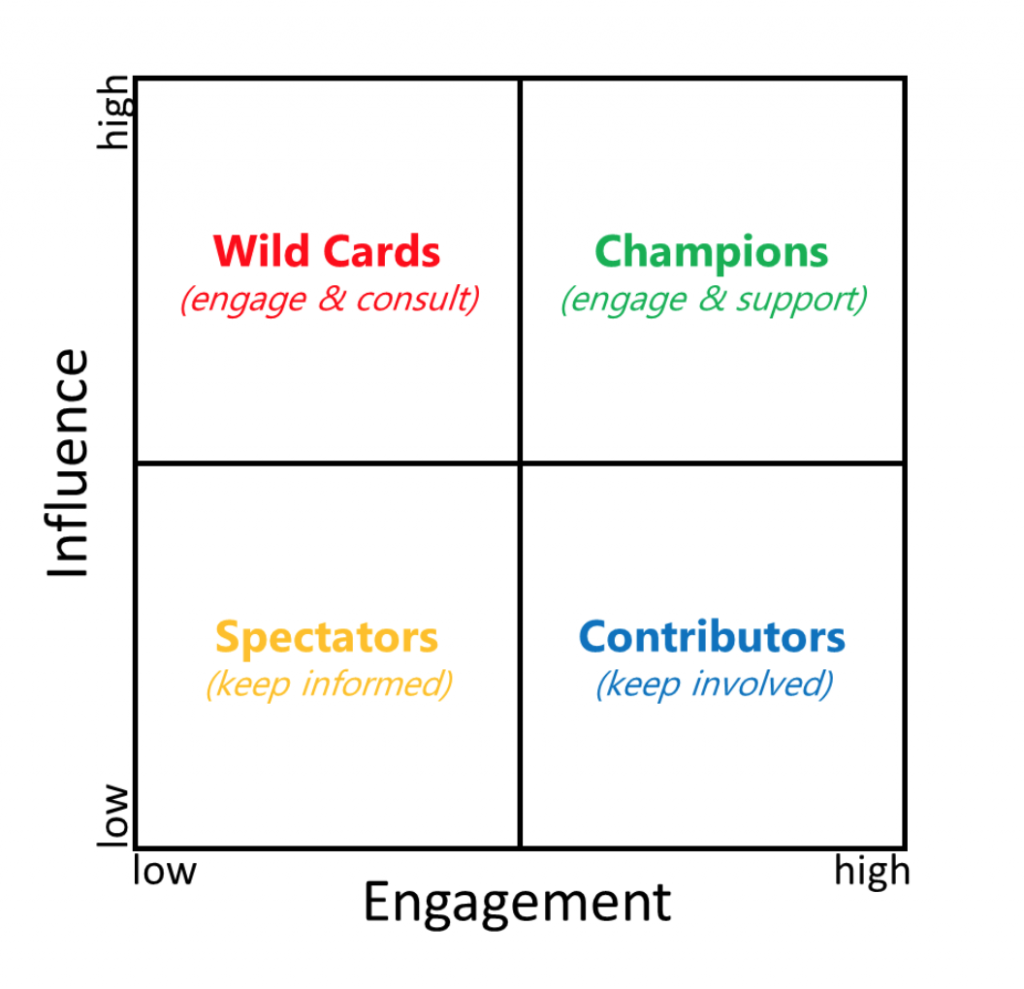
Identity and Access Management (IAM) is a unique IT solution because of its far-reaching scope. IAM touches everyone and everything in an organization. Its reach extends from HR processes to the physical and system access of each individual. Once IAM goes live, the entire employee lifecycle is driven by the HR team and how they […]
Mastering Identity Management: Is HR Creating a Hostile Work Environment? Read More »