Idenhaus Cybersecurity Services
Learn how Idenhaus can help
your organization mitigate
its cyber risk and liability
Hackers Are Working Around The Clock.
Are You Ready?
Organizations are confronting increasingly sophisticated and unrelenting cyber threats from entities that are intent on finding and exploiting vulnerable targets.
Because time is of the essence, Idenhaus’ experts go to work immediately to solve your most challenging cybersecurity problems and help you answer key questions about your level of preparedness. For example:
- Do you understand the impact to your business and customers if sensitive data is breached?
- Are you using effective tools to monitor data use and enforce security policy?
- Have you implemented a training program to educate your employees, contractors, and partners on cybersecurity?
We also lower project costs by identifying the most effective IT spend to address your organization’s most critical cyber threats with appropriate countermeasures.
Contact us to learn how we can help you improve your security profile and approach to risk management.
Don’t give hackers free reign to pillage your information and assets.
243 DAYS
(8 MONTHS)
83%
Top 3 threats to their business
We'll Quickly help Identify And Address Your Cyber Risk
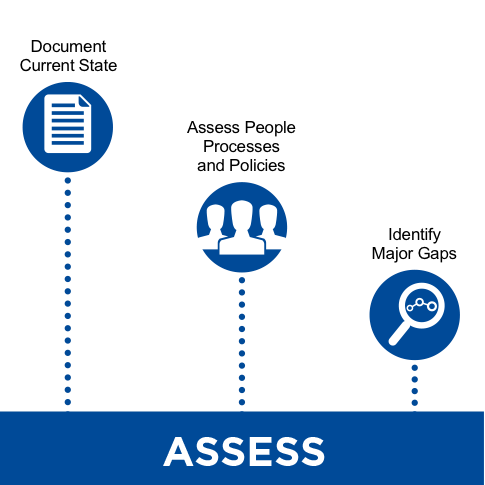

Phase one: Discovery and Assessment
- Risk Management and Oversight
- Incident Response
- Threat Intelligence and Collaboration
- Legacy System Evaluation
- Technological Cybersecurity Controls
- Procedural Cybersecurity Controls
- Personnel Skills Evaluations
- Initial Cyber Assessment using appropriate framework (NIST, ISO 27001, CIS Critical Security Controls)
- Periodic assessments to monitor environment and support maturity of security capabilities
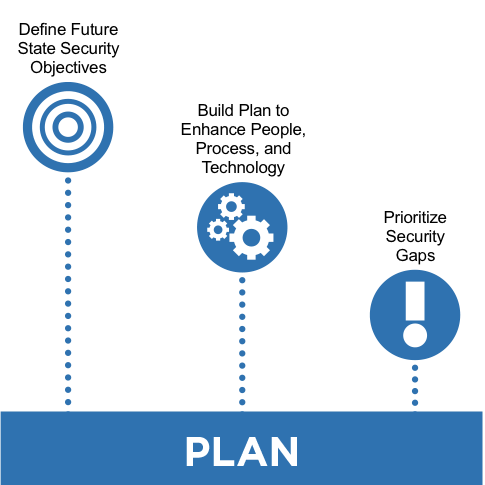
Phase Two: Analysis and Recommendations
- Business Impact Profile (Key Business Concerns)
- Cyber Security Assessment (Policies, Programs, Procedures, and Technology)
- Risk Management Strategies
- Cloud & Mobile Security Strategy
- Solution Architecture and Technology Options
- Develop Training Strategy and Security Awareness Program

Phase Three: Resource Planning and Implementation
- Resource Plan – Determine the mix of internal and external resources required to deliver the work
- Budget – Cost estimates and project business case
- Timeline – Develop project plan and identify critical dependencies between projects
- Actionable Plan to address issues
Cybersecurity Resources
Schedule your Cybersecurity Assessment
Cybersecurity Assesment
Subscribe to our Newsletter
Our Latest Tweets
Utilizing CSF to Manage Cyber Risks - via MedTech Intelligence @MTI_editor
Are Passwordless Systems The Future Of Authentication? via @TechRadar
5 Easy Ways To Boost Your Cybersecurity Protection via NH Business Review
