This week’s IAM and cyber security roundup covers security tools, NERC CIP v5, hospital hacks, Identity Management UX, and more. From February 22 to March 8, 2016, here are the five articles that made the cut.
1. Why Your Security Tools Are Exposing You to Added Risks
The overall lesson from the last 12 months of security product vulnerabilities is that whenever a new piece of software or device enters your network you must ask “what are the consequences of someone using this against me?”
The big lesson from 12 months of security product vulnerabilities: there’s no foundation of trust in any piece of software. They all represent a potential new attack vector. Read now >>
2. Is Your CISO Out of Place?
“To whom CISOs report and what access and influence they have are as important as their qualifications and experience. The role must be senior enough for the CISO to gain the respect of C-level executives and the board.” – The Wall Street Journal
Cyber risks don’t respect the functional boundaries of the organization. From a cyber perspective, what one side of the enterprise does impacts the cyber risk levels of the entire business. Read now >>
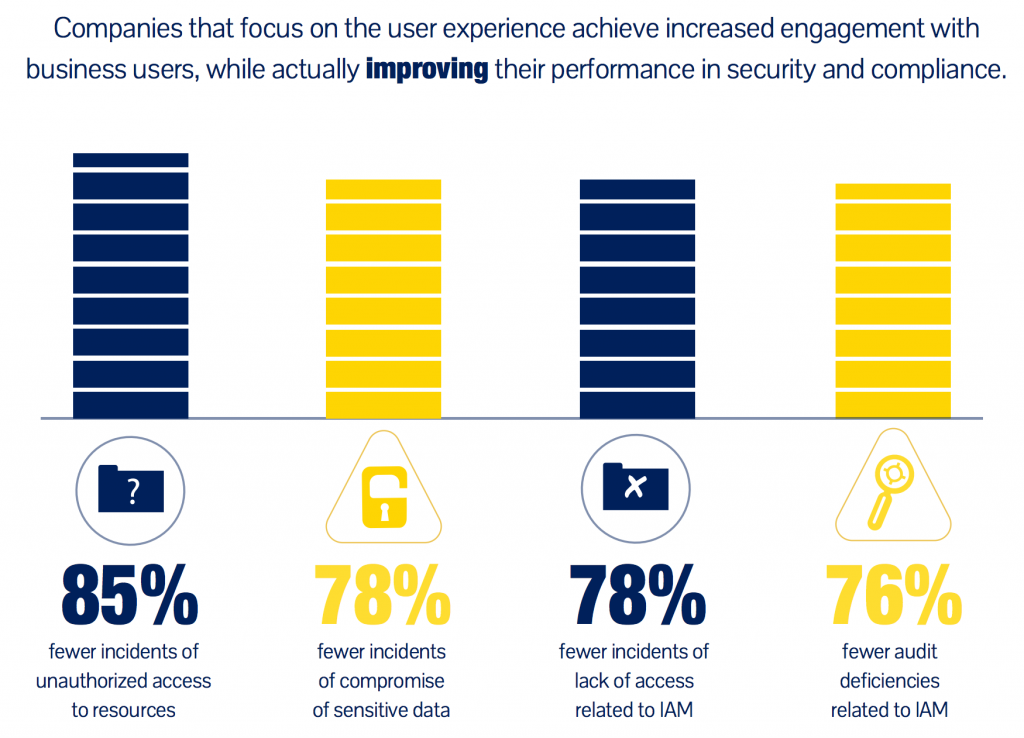
3. IAM for Everyone: Bridging the Gap Between the IT-Savvy and the Business User [Infographic]
IAM interfaces and processes can no longer be oriented toward IT. They must be simple and intuitive for all business users, using familiar terminology, so users can easily request the access they need…when they need it.
Aberdeen research showed that a focus on the extended enterprise business user can result in a 60% improvement in user productivity, and an 80% improvement in user satisfaction! View now >>
4. FERC’s Delaying of NERC CIP V5 Implementation Reinforces Need for Strong Cybersecurity Culture
“I’m concerned about the perception these types of decisions create. The electric industry is full of hard working, incredibly dedicated people who want to do the right thing. But that thing keeps changing.”
This delay underscores the need for the energy industry to create a security culture that prioritizes the mitigation of dangerous and frequent cyber threats over the politics that hinder even the most well intentioned industry standards and guidelines. Read now >>
5. Patient monitors altered, drug dispensary popped in colossal hospital hack
“The attack scenario is harrowing: Diligently executed, many human lives could be at stake, and extrapolating this problem to other hospitals is even more worrisome.”
Security researchers have exploited notoriously porous hospital networks to gain access to, and tamper with, critical medical equipment in attacks they say could put lives in danger. Read now >>
[Bonus] Chuck Brooks on Cybersecurity: The Weakest Link Will Always Be the Human Element
“The real danger is that the Internet was not built for security at its inception; it was built for connectivity.”
This was our most popular article on Twitter. Cybersecurity expert Chuck Brooks talks about where we stand in what many people call the “wild, wild west” of cybersecurity. Read now >>
If you enjoyed these articles, subscribe to the Idenhaus Cybersecurity Newsletter.
You may also like…
Does your Identity Management Program Pass the ‘Marshmallow Test’?