Access security can feel like chaos.
To help bring some control to the chaos, Jerry Combs, Principal Identity Architect at Idenhaus Consulting, and Kent Purdy, Solutions Marketing Manager at NetIQ, joined forces to discuss pressing access management challenges facing organizations today in “Taking Chaos Out of Access Control”. During this 54-minute webinar, Jerry and Kent identify common security architecture flaws and provide actionable advice on how organizations can shift from an accidental architecture to a strategic, service-based architecture.
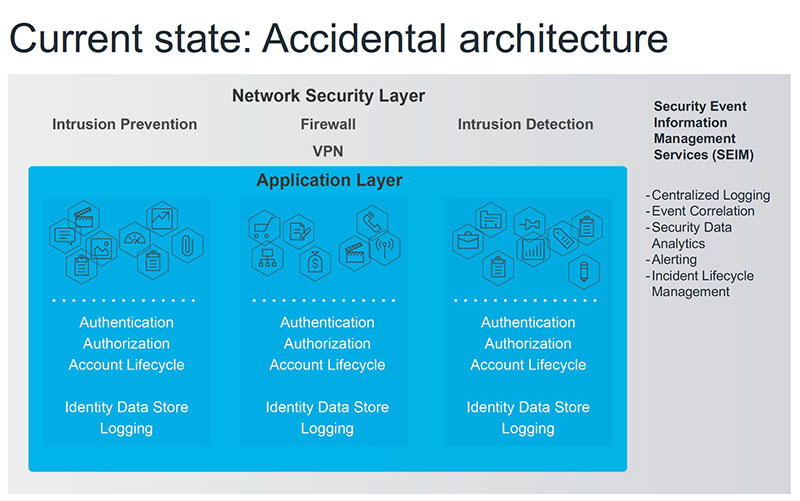
Many organizations have developed an accidental architecture over time, which causes several problems:
- Multiple applications and platforms
- Disparate back-end apps
- The user account lifecycle is an afterthought
- Not scalable
To construct strategic, service-based architecture, Jerry recommends using the Access Security Layer Approach, which is a simpler, more flexible way to handle access security that protects all access points and improves the customer experience.
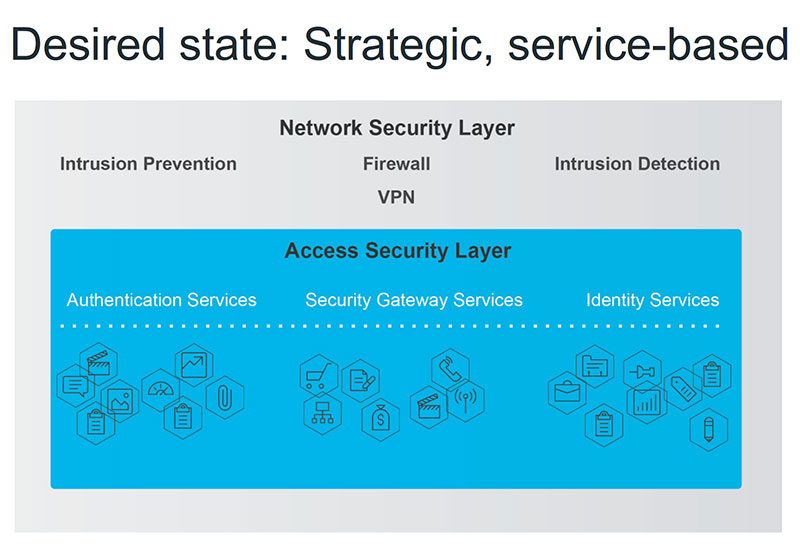
The desired, strategic, service-based architecture accomplishes important goals, such as:
- Supports any user, device, and location
- Fully managed and secured
- Comprehensive
- Flexible
- Works with past, current, and future tech investments
Lastly, Jerry and Kent outline how to overcome the B2C access challenge of giving consumers access at massive scale without compromising security.
Click here to watch Taking the Chaos Out of Access Control.
If you enjoyed this post, signup for our popular IAM biweekly newsletter and our biweekly healthcare IT newsletter, delivered Tuesday evenings. Follow @Idenhaus on Twitter.
By going to work quickly to solve the most challenging cybersecurity and identity management problems, Idenhaus takes the pain out of securing corporate information and assets for companies that aspire to maximize their potential in this digital age. Contact us today!






