Why do so many Identity Management implementations fail the first time?
Identity Management (IAM) solutions often fail to deliver results because organizations do not develop a Data Map up front as part of their Requirements and Design.
Create Data Maps – Define the flow of data from the Authoritative Source to the Central Repository and on to Active Directory. This will make it clear where the data originates, where it is going, and make sure that the data flow is accurate and that any transformations are well understood.
– 8 Tips to Build a Solid IAM Foundation
A Data Map defines how user data will flow across connected systems and support identified use cases. As such, Data Maps are an essential component to implement any successful IAM solution.
Unfortunately, developing a Data Map is often overlooked in the rush to deploy the technology as quickly as possible. The end result is that organizations do not realize the security and efficiency benefits their IAM systems can deliver and, instead, resort to workarounds to bridge the gaps. These workarounds drive up operating and support costs and represent a lot of value left on the table. A Data Map is critical because it makes the implicit solution characteristics explicit for the implementation.
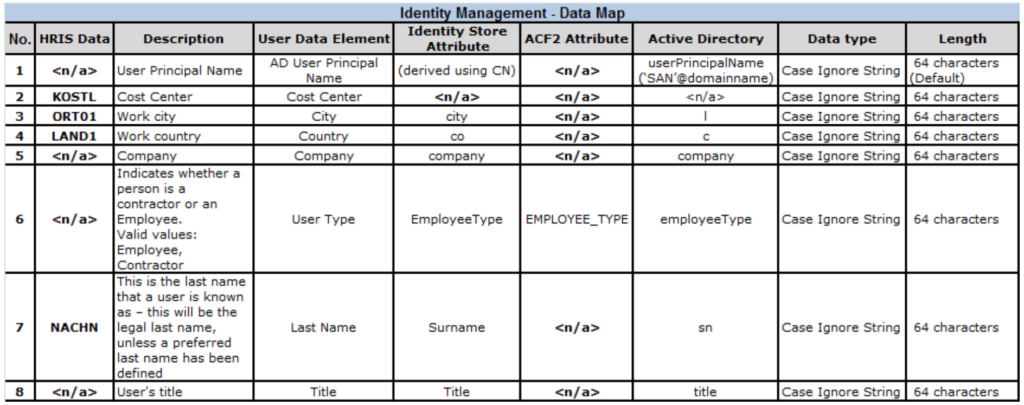
Data mapping begins with the identification of key user attributes and then matching those attributes between authoritative sources and downstream data consumers. For example, mapping user data between the HRIS system and downstream systems that contain the same data elements but call them by different names. This matching enables the IAM solution to correctly exchange user information, properly manage organizational relationships (e.g. managers and approvers), support logging and auditing functions, and properly enforce security policies.
Data Maps are created between the Authoritative Source, the IAM directory (or Identity Store), and downstream systems and databases. The scope of the data map is defined by the use cases that it supports. When creating a data map, it’s a good idea to begin with the Onboarding use case for your baseline data set. Begin by answering the following questions:
- What data do we need to Onboard an employee and provision their access and assets?
- Network access
- Workstation provisioning
- Approval workflows (manager, cost center)
- Personalization (name, title, contact information)
- Email (name, title, username, organizational data)
- Physical Access (e.g. security badge system)
- What is the minimum set of data necessary to create a working network account?
- When are the data available in the onboarding process? Is there any impact to asset provisioning, provisioning network access, or creating an email account?
Here is a short sample of a data map that lays out the attribute flow:
They say the devil is in the details and that is certainly true in any enterprise-class IT solution. Identity Management solutions directly impact the user experience for good, or bad. When these experiences are negative, they tend to leave a mark and it can be very challenging to recover. For this reason, it’s important to get your foundational user data correct out of the gate.
A Data Map provides a proven path to better data and better outcomes. Surprise and preparation very rarely go together, and it’s best to avoid a bad result by investing a bit more in the analysis phase of your project.
If you liked this article, you’ll LOVE this free digital book I just published on the top challenges that companies face when implementing Identity Access Management and how to overcome them. It’s titled “Re-Imagining Identity Management In The Digital World: How To Design, Choose And Implement The Right IAM Solution For Your Business” and you can grab it for free here: Click to download!
Follow @Idenhaus on Twitter and subscribe to our biweekly newsletter.
By going to work quickly to solve the most challenging cybersecurity and identity management problems, Idenhaus takes the pain out of securing corporate information and assets for companies that aspire to maximize their potential in this digital age. Contact us






