“If you fail to plan, you are planning to fail!” – Benjamin Franklin
Planning for cybersecurity success may be the biggest obstacle for any organization to overcome. Why? Because planning is usually treated as a ‘bolt-on’ measure and not given the attention it deserves. Done correctly, a plan serves as a framework to define the organization’s security objectives, initiatives, and targets and aligns security strategy with the organization’s actions. Ultimately, the key to building new security capabilities and executing a cybersecurity strategy successfully is to have people in the organization understand the plan from the top down.
The issue with cybersecurity planning is not that it is not being done at all; rather, the issue lies in how the planning exercise itself is executed. Most organizations look at planning through the lens of incremental improvement to their existing security measures and their current network infrastructure. These legacy systems act as an anchor that bogs down the planning process by focusing too much on what is easy, such as enhancing what the organization already has, and not enough on where the organization needs to be.
The only problem with that narrative is that it can be very difficult to shift an organization’s culture and change its thinking. First, there needs to be an internal Champion who is spearheading the initiative to approach planning in a new way. Second, support from leadership is necessary to allocate the budget and personnel for a ground-up review. Last, leadership needs to communicate the vision for the cybersecurity program to gain buy-in and support from the front lines. Many organizations feel they are unable to move forward in a timely manner and essentially settle for incremental change over building a mature cybersecurity program.
Legacy systems act as an anchor that bogs down the planning process by focusing too much on what is easy, such as enhancing what the organization already has, and not enough on where the organization needs to be.
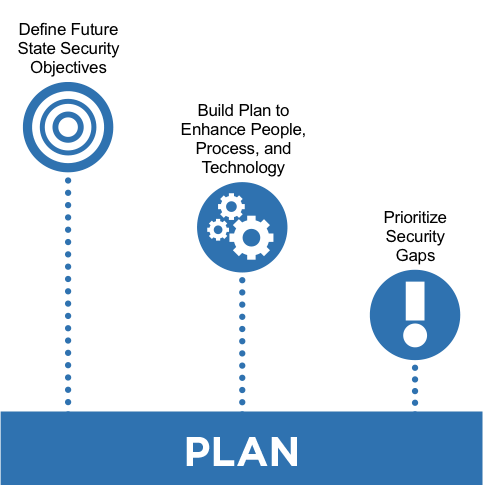
Given these challenges, how does an organization go about planning and designing a mature cybersecurity program? The best answer is to use a formal, phased approach like the one outlined below.
4 Steps to Planning for Cybersecurity Success
1. Current State Assessment
To properly plan a cybersecurity program, it is best to invest in a bottom-up review and design. Assessing the current state of your organization establishes a baseline understanding of the security foundation and is important to identify gaps in your capabilities. A good cybersecurity program will be designed using policy and procedures to define how to conduct the program and then build into a technical architecture and resource allocation to meet that plan. It is also a good idea to include is organizational readiness assessment during this step.
2. Define Future State (Vision)
Identify a portfolio of security projects/opportunities that address the issues and gaps identified the Current State Assessment. This is a good point involve executives to communicate the learnings, define the program at a high level, and start developing executive support.
3. Develop Plan
Prioritize and develop opportunities including stakeholder analysis, resource requirements, required technical architecture and resources, and define a program plan that identifies individual opportunities and dependencies between projects. When planning for a cybersecurity program the planners need to understand the business objectives, the regulatory environment for their information systems, and the customer base utilizing the business. A good, solid understanding of the requirements necessary for the cybersecurity program allows for the identification of what aspects of cybersecurity need to be prioritized and which protection mechanisms need to be implemented to support those requirements.
4. Finalize
Develop executive presentation with recommendations for using outsourcing, hosted-services, or in-house IT. The plan will identify technical/ operational solutions to address any infrastructure issues, estimate level of effort, timeframe, and cost for all of the potential solutions, and classify the solutions based on technical complexity, timeline and cost of implementation. Further, the plan should identify short-term and long-term solutions and any quick-hit savings areas. Based on this information, the Plan with tasks and timelines will be prepared.
A successful planning exercise accounts for the fact that all of these issues are critical to the implementation process. More importantly, successful organizations understand that not accounting for every issue leads to a strategy that falls short. Organizational readiness, which focuses on the soft issues of change management and process change (including organizational impact), and technology gaps, describing the “hard issues” of IT architecture and infrastructure to support a new strategy, are some of the key deliverables derived from the planning process. They are integral to prioritizing the next steps and phasing of a project.
Successful organizations understand that not accounting for every issue leads to a strategy that falls short.
Key Deliverables in a Cybersecurity Planning Process
- Understand current security capabilities including process, technological and organizational capabilities. Develop a common understanding of key issues, constraints, strengths, and opportunities.
- Collect, document, and organize existing, planned, and potential initiatives/opportunities.
- Co-develop criteria by which these opportunities can be categorized, sorted, evaluated, and prioritized. Conduct prioritization sessions with key stakeholders and leaders to arrive at initiative phasing.
- Create an integrated plan to implement the required process, technology, and organizational capabilities required. Develop success metrics and change management plans necessary for effective transformation.
- Secure the necessary sponsorship and resources.
As organizations are faced with increasingly sophisticated and unrelenting cyber threats, proper cybersecurity planning is more important than ever. By following the process outlined above, your organization can take the first step to building a mature cybersecurity plan.
Click here to subscribe to our blog and follow @Idenhaus on Twitter.
Photo credit: Flickr
By going to work quickly to solve the most challenging cybersecurity and identity management problems, Idenhaus takes the pain out of securing corporate information and assets for companies that aspire to maximize their potential in this digital age. Contact us today!