
“This year, security professionals seem confident in the tools they have on hand, but they are uncertain about whether these resources can help them reduce the operational space of adversaries.” — Cisco 2017 Security Capabilities Benchmark Study
With 110 pages of fascinating (and disappointing) cybersecurity statistics, it’s easy to get lost exploring Cisco’s 2017 Annual Cybersecurity Report. A core component of the annual report is Cisco’s Security Capabilities Benchmark Study, which offers insights on the maturity level of security operations and security practices currently in use. The third annual study included over 2,900 CSOs and security operations managers across 13 countries. While there were dozens of noteworthy findings throughout the report, here are three interesting stats that caught my attention. You can download Cisco’s 2017 Annual Cybersecurity Report here.
1. Leadership Commitment to Cybersecurity Continues to Decline
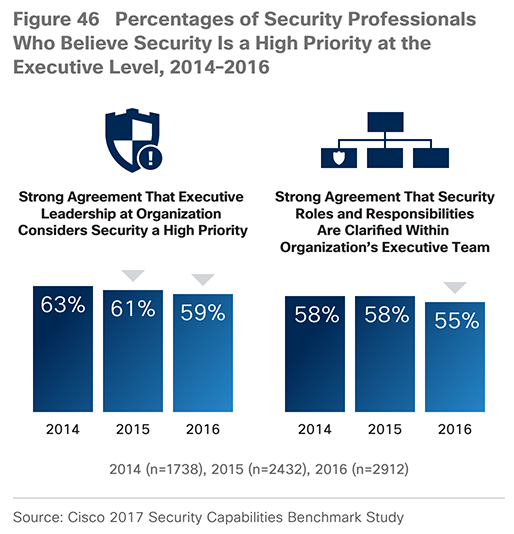
The percentage of security personnel who responded affirmatively that cybersecurity is a high priority for their organization declined from 63 percent in 2014 to 59 percent in 2016. This change is surprising given the heavy emphasis on breaches and cybersecurity in the media. It may be a reflection of cynicism on the part of security professionals or the resource allocation decisions of executives, or a bit of both.
2. Security Alert Response Rates Are Awful
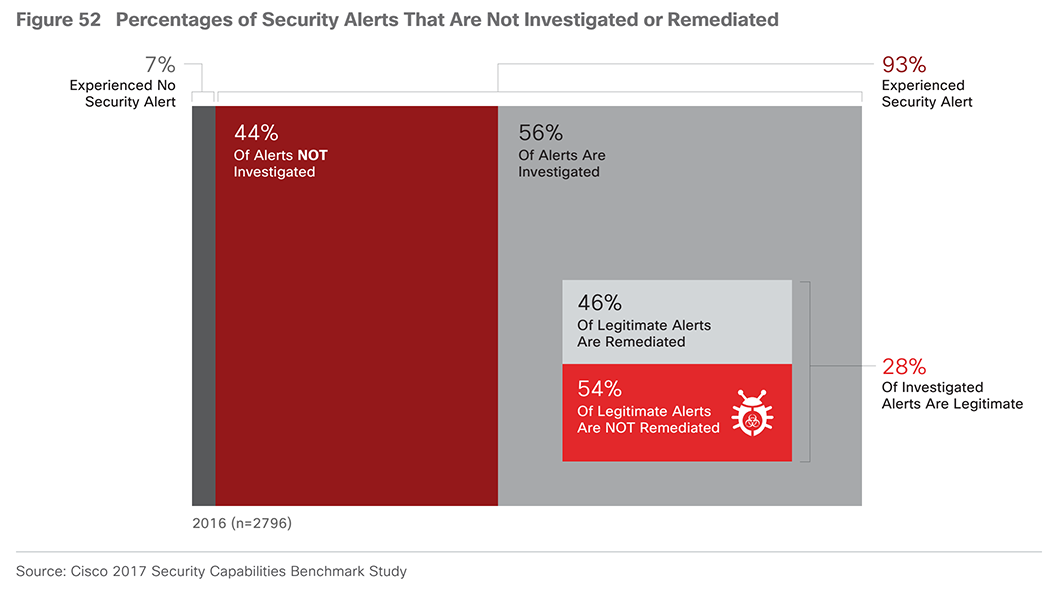
In 2016, only 56 percent of alerts (on average) were investigated by a company, and of those legitimate alerts, 54 percent were not remediated. The numbers are staggering. There may be a variety of potential contributing factors for this statistic, but the chief reason is understaffing. The talent shortage in cybersecurity is well known, and these numbers are indicative of an industry that does not have enough personnel and resources.
Security professionals are forced to skip the investigation of alerts simply because they do not have the talent, tools, or automated solutions available to determine which ones are critical and why they are occurring. — Cisco 2017 Security Capabilities Benchmark Study
3. Data Breaches Drive Change

The survey revealed that 90 percent of the security professionals reported that a breach drove changes that improved their companies’ security postures. Organizations are clearly taking a reactive approach to cybersecurity, only enhancing their capabilities after a breach.
The growing number of security breaches are also driving regulatory changes in some countries. For example, the EU’s GPDR legislation defines strict rules for data residency and ownership with stiff penalties for companies that fail to comply. Large players such as Microsoft have recently opened new international data centers, where laws require cloud data to be kept within the country. While the data may still reside in the country of origin, the threat from hackers still remains.
Faced with real and immediate effects like lost revenue and customers, organizations can no longer simply wish away gaps in security protection, because the question is not if a breach will happen, but when. — Cisco 2017 Security Capabilities Benchmark Study
It is essential for companies to focus on establishing an integrated and simplified approach to security. However, considering that only 59 percent of CSOs feel that leadership views cybersecurity as a high priority, cybersecurity leaders must learn how to clearly articulate business drivers to executives and stakeholders before a breach occurs.
Click here to subscribe to the blog
Follow @Idenhaus and connect with Hanno on LinkedIn.
By going to work quickly to solve the most challenging cybersecurity and identity management problems, Idenhaus takes the pain out of securing corporate information and assets for companies that aspire to maximize their potential in this digital age. Click here to contact us






