
“Standardization is the necessary foundation for improvement.” – Henry Ford
Henry Ford is credited with revolutionizing manufacturing – dramatically increasing productivity and reducing errors/waste in the process. How did he accomplish this modern miracle of manufacturing? The secret sauce was standardization! By using interchangeable parts required to make the individual pieces of the car, each car was the same every single time. All pieces fit with all the others – any part would fit any engine and any engine would fit any chassis. The standardization of parts made it possible to break down assembly of the Model T into well-defined steps. Assembly line production was more efficient than having each worker make a complete automobile, and standardized, interchangeable parts made this new way to organize production possible.
We can apply these same lessons to Identity Management and, as a result, deliver more value from our solution in less time. Standards liberate us from having to make decisions about those parts of the IAM solution and connected systems where there is little or no scope to add value. Standards in data quality, processes, policies, and workflows are all important. The time and effort saved can then be applied to those provisioning tasks that matter most, which leads to either more value delivered or less time/cost expended. In other words, standards allow us to systematize routine tasks so that the valuable work can happen on top of them.
Organizations with less than a thousand users can manage access and assets with largely manual processes, which work reasonably well on a small scale. That said, these ad hoc provisioning tasks are prone to data entry errors and other mistakes and are more likely to require re-work. These mistakes risk disrupting business users if they lose access and will require skilled IT workers to resolve incidents and maintain/support the solution. The complication with ad hoc processes is that they do not scale, are error prone, have inconsistent outcomes (e.g. time to provision varies, access is not granted at the same level each time) and are expensive to support. With enterprise-level standards; however, we can free our IT staff from having to decide how to configure each user and which policies apply to the user’s role. The standards allow us to move from an Ad Hoc to a Standardized Provisioning model that automatically provisions users the same way each time based on a set of defined rules.
Advantages of standardization include:
- Provisioning processes become more reliable and variations in outcomes diminish
- Decreasing administration expenses for both systems and processes
- Supporting more users with fewer IT resources
- Evaluating IAM solution performance over time becomes easier, supporting continuous improvement of the processes and technologies
- Building credibility for the IT organization and convincing the business to engage and adopt standard management models (i.e., Center of Excellence vs Shadow IT)
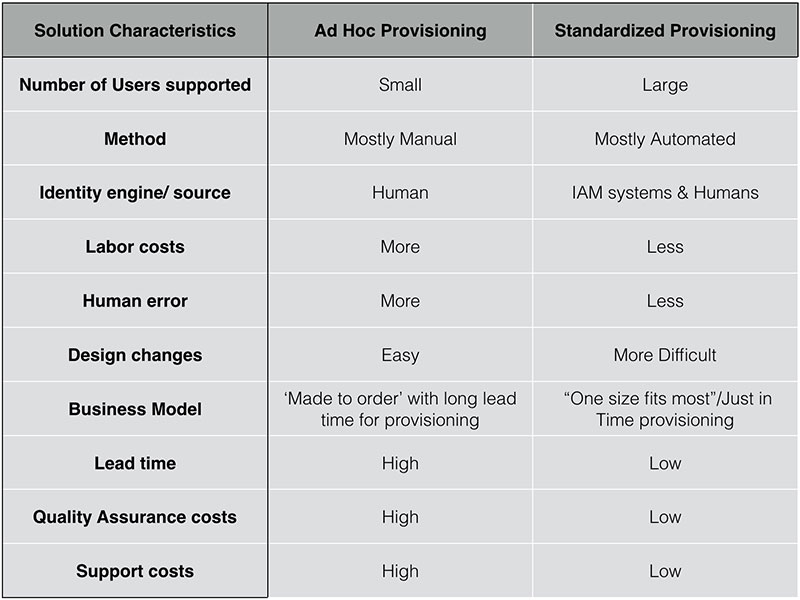
The table below compares Ad Hoc Provisioning (largely manual, few standards) against Standardized Provisioning (largely automated, well-defined standards) and their relative characteristics.
Ultimately, IAM solutions provide a platform for organizations to automate routine provisioning tasks so that little to no manual intervention is required unless there is an error. Standardization can greatly improve process performance, lower maintenance costs, and give senior management more control over IT operations.
So how do we get there? Standardization needs support from senior management, which establishes standardization criteria and ensures that the focus remains on performance improvement. An Organizational Efficiency (Six Sigma/Lean Six Sigma) team can manage standardization as a part of its portfolio of process improvement projects. IT standardization should follow process standardization, not the other way round.
If you enjoyed this post, please share with your network and follow us @Idenhaus. Subscribe to weekly updates here.
Photo credit: Flickr
By going to work quickly to solve the most challenging cybersecurity and identity management problems, Idenhaus takes the pain out of securing corporate information and assets for companies that aspire to maximize their potential in this digital age. Click here to contact us today!







2 thoughts on “Why Standards are the Secret Sauce to IAM”
Absolutely agree with you standards are important in large organisation be it IAM and data security or Information assurance security. However they need to be thought through practicle logical to follow and implement.
We completely agree that standards need to be practical and appropriate to the needs of the organization. Establishing a proper Governance structure that incorporates the needs from across the organization (security, networking, operations, accounting/finance, etc.) is an essential first step in defining and adopting organizational standards.