Since the inception of Cybersecurity twenty-plus years ago, the industry has gone through a plethora of iterations. The Internet was initially designed to be an open environment to enable information sharing between academics and researchers. When businesses and government agencies joined the network explosion in the late 1990s, the open environment turned into a security nightmare. Security was not part of the original intent or design; it was an afterthought—what the creators added when they realized their project was missing something. Because of this design, a defense-in-depth approach to cybersecurity was born; that is, the principle of layering security mechanisms to increase security of the system as a whole. If an attack causes one mechanism to fail, other security layers are in place to protect the system.
A simple view of the original defense-in-depth design is shown below. Based on the diagram, it’s easy to understand why this model works in theory.
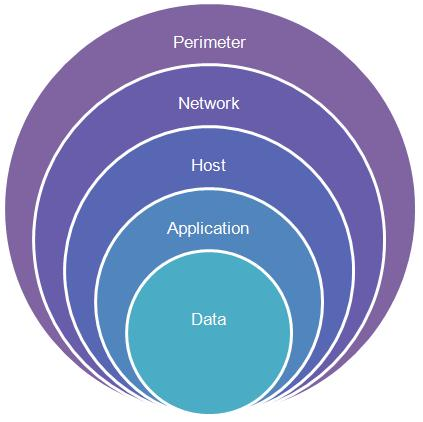
Defense-in-Depth example from tech-wonders.com
However, the rapid acceleration of cybersecurity needs has resulted in thousands of security vendors. Over the past five years, $7.3 billion had been invested into 1,208 private cybersecurity startups. This influx of services and software has overwhelmed IT and security professionals with ‘vendor overload.’
“Over the past five years, $7.3 billion had been invested into a whopping 1,208 private cybersecurity startups.” —CB Insights Report 2015
In addition to the exploding number of security vendors, another trend has emerged that is contributing to the technology overwhelm felt by CISOs: a growing shortage of trained cybersecurity professionals. Specialized cybersecurity skills around cloud computing represent the biggest gap. While these two trends may seem mutually exclusive, they actually go hand-in-hand. The lack of experienced security pros has left CISOs stranded on an island, unable to receive intelligent input from differing viewpoints. A CISO has a large set of responsibilities inside a company and the additional burden of reviewing the ever changing technology landscape is causing CISO burnout.
To prevent technology overload, security leaders must take a defense-in-depth approach and develop a clear, strategic plan based on business needs that addresses each layer of the security onion. By beginning with the business needs—not the technology needs—CISOs can focus their efforts on creating a well-defined, comprehensive strategy before speaking to vendors.
When thousands of vendors are beating down the door for a “quick demo,” it’s easy to lose site of the end goal — a secure network. Lack of time, lack of talent, lack of resources, and inability to stay informed on the technology landscape are enough to overwhelm even the most seasoned cybersecurity professionals.
Here are three tips to help mitigate vendor overload and keep your eye on the prize.
1. Understand your network and your business needs first
While this may seem like common sense, it may be the hardest part of any cybersecurity professional’s job. Organizational silos and lack of integrated software make this a difficult process. More often than not, defining the security environment is usually a tack-on affair and not an in-depth analysis of the overall business needs. This often results in a disorganized and fragmented approach to security—throwing technology solutions at problems without an understanding of how it will affect the overall network.
“(At a product pitch,) ask all stakeholders to be present to provide input – not just the security team, but personnel from procurement/acquisition, finance, enterprise architects, etc.” —Dan Waddell
2. Prioritize efforts based on business needs
The technology overload combined with the lack of trained cybersecurity professionals result in decisions which seem correct at the time but provide redundant or superfluous security. In the past ten years, software specific to the host, application, and data layers of the security onion has emerged. However, the majority of security offerings still address the perimeter layer. Employing defense-in-depth principles and focusing on the necessary tools to secure each layer of the network not only makes it much harder for an attacker to compromise the network but also prevents CISOs from ending up with three products that protect the perimeter. Once the business needs have been defined, your efforts must be prioritized based on impact and importance to network security. An e-commerce business would likely prioritize the protection of the public facing website and customer data whereas an international consulting firm would focus on securing internal communications across geographic regions and mobility management.
3. Don’t get attached to vendors or devices
This may be the most important one. Just because you have always used the same vendor, software, or security device, it doesn’t mean you still need it. Just because an IDS was deemed necessary doesn’t mean it still is. Decaying technology can leave your organization more vulnerable. On the other end of the spectrum, throwing new technology in the mix may seem easier in the short term. However, without proper assessment and alignment with overall security strategy, cobbling together technologies leads to a more complex and less efficient IT team.
“An additional challenge is that there is a growing tendency to cobble together a patchwork of technologies that don’t work well together; leaving IT administrators with a set of automated reports to reconcile the differences between products.”
—Challenges in Selecting an IAM Solution
Every few years, organizations should do an in-depth review of their technology and how it addresses business needs. This review should be used to plan budgets, clarify strategy, and make informed technology decisions. Technology changes and the needs of the business change. Getting attached to technology is a sure way of being behind in the efforts of protecting your networks.
If you’d like a comprehensive view of vendor evaluation best practices, check out Mastering Identity Management: A Better Process for Vendor Evaluation.
Follow @Idenhaus and subscribe to our biweekly Identity Management and Cybersecurity newsletter.
Photo credit: Flickr






