
The Fortress of the Knights, located in Syria, was one of the most impenetrable, secure castles in history. The surrounding land steeply slopes away, making access to the castle difficult and rendering traditional invasion methods ineffective. But, in 1271, it finally fell to a group of Muslim sultans who used stealth to take down the castle.
In a great feat of social engineering, the sultans created a fake document stating that the castle’s grand commander in Tripoli had ordered the troops to surrender. The Knights believed the proclamation and handed over the fortress to the enemy.
“While our defenses need to be 100% effective, the offense or attackers only need to be successful once.” – Major General Brett Williams, USAF, (Retired)
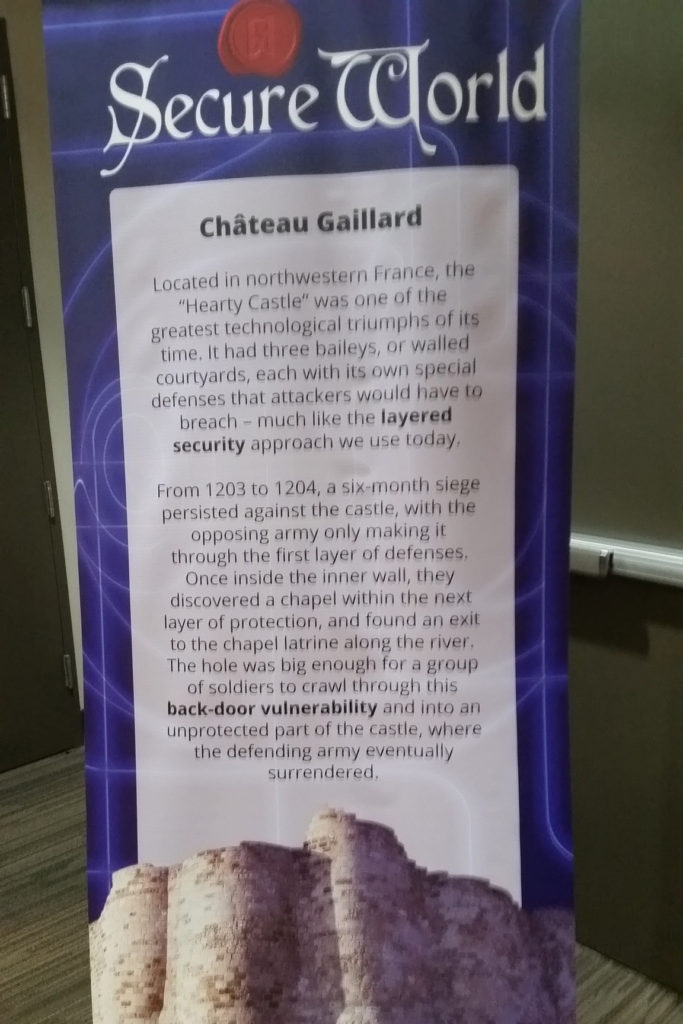
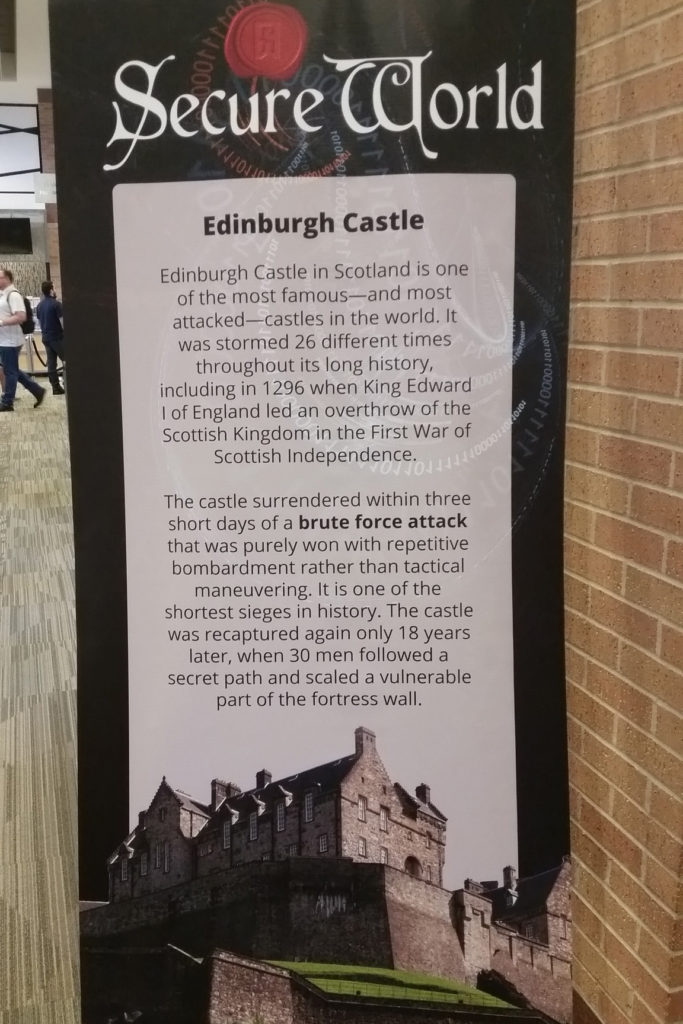
Medieval castle defenses were the main theme of SecureWorld Dallas 2017, which I recently attended to learn more about the latest defenses and cybersecurity threats facing information systems.
Just like castle defense systems were used to protect the people and treasures of the kingdom, today’s cybersecurity defense systems guard valuable corporate and consumer data.
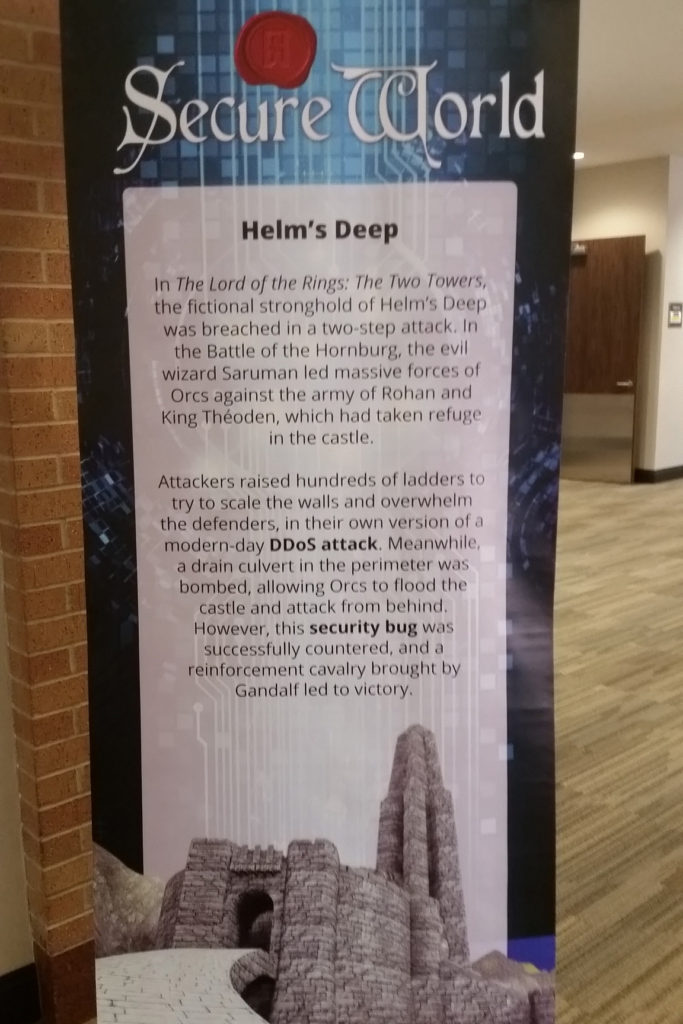
The theme was most appropriate, as it repeatedly showed that no matter how many new defense systems castle builders devised, the threats simply would escalate their attacks to overcome them.
Castle architects leveraged high places, high walls, towers, moats, drawbridges, murder holes, embrasures and many other tactics to secure the inhabitants and assets. However, as technologies for defense improved, so did the offensive weaponry.
In the end, gunpowder and iron cannons proved to be the undoing of such centralized security positions. These strong and accurate mobile offensives deterred invasions. Observance and strength with mobility to respond to new threats was an effective means of securing their kingdoms, so civilized societies began to urbanize and build fewer castles.
We are witnessing the same evolution of data centers and information systems architecture. Originally, a centralized data center with physical security systems and dedicated telecommunications seemed to provide a decent level of assurance. We only had to protect ourselves from ourselves.
Then the Web opened up to the marketplace. Organizations that didn’t have a strategy to open business systems on the Web were at risk of missing out on growth and new opportunities. So, companies raced to market and built castles in the cloud to secure corporate and user assets. With massive breaches like Equifax and Yahoo making headlines, it’s evident that our castles in the cloud are no longer effective against modern threats.
Here are five takeaways from SecureWorld Dallas 2017.
1. Security Teams > Technology
Finding and building skilled IT security teams that are passionate about deterring breaches is just as important, if not more so, than the technologies being used to defend digital assets.
2. Corporations Cannot Rubber-Stamp Cybersecurity
Risk Mitigation and Response Strategy cannot be rubber-stamped.
- The CEO must set a culture for valuing and protecting the corporate and customer assets.
- What will you do when your systems take a fatal hit? Do you have your emergency response team defined? Do they practice the breach response policies and procedures?
3. GDPR Is Regulatory Challenge for US Organizations
As if Privacy Shield isn’t enough, GDPR is the new EU regulatory challenge to all systems that maintain personally identifiable information and can affect US organizations.
- Has your compliance team reviewed the requirements for GDPR?
4. Encryption Algorithms Have Evolved
Cryptography is changing and not using the correct ciphers can lead to major threats.
- Some older encryption algorithms are no longer secure (RC4/WEP). Have you measured the risk you’re exposing if these encryptions are still in use?
5. Cybersecurity Isn’t Set-It-And-Forget-It
Continuous security monitoring, threat detection, incident reporting, and effective response is the key to an organization achieving successful security and growth on the Web.
Castles became a thing of the past because modern threats deemed them less effective and turned them into death traps. We’re seeing the same thing happening now. Cloud computing infrastructure needs to find a better foundation for protecting its digital assets, and maybe new foundational tools like blockchain based DNS can help.
No matter how many new defense systems castle builders devised, the threats simply would escalate their attacks to overcome them.
Check out the list of upcoming SecureWorld events – it’s an excellent opportunity for cybersecurity professionals to stay informed of the latest threats.
This article was authored by Ron Bowron.
Follow @Idenhaus on Twitter and subscribe to our biweekly newsletter.
Photo credit: Flickr
Learn more about the top challenges that companies face when implementing Identity & Access Management and how to overcome them in our new book:
Grab it for free here: Click to download!
By going to work quickly to solve the most challenging cybersecurity and identity management problems, Idenhaus takes the pain out of securing corporate information and assets for companies that aspire to maximize their potential in this digital age. Contact us






