Thanks for reading our biweekly roundup of Identity Management and Cybersecurity newsbites. We curate a diverse selection of IAM, IDaaS, Access Control, and RBAC articles to help you navigate the rapidly-changing IT security landscape. Subscribe to our biweekly newsletter here.
RSA 2019 Highlights: Security Challenges Moving to the Cloud via Idenhaus
One of the fundamental changes is the shift in technology from physical servers to virtual servers and then from virtual servers to Cloud servers.
An Inside Look at New York State Government Cybersecurity via GovTech
“Part of [our plan] was making sure cyber security was firmly at the table in budget planning. Our approach was more a conversation about cyber as an element of enterprise risk management. We provided relevant examples of the growing risk of cyberattacks, and associated costs of incidents and breaches. We also examined and tracked spending in ways that provided a clearer picture of initiatives across the organization that support enhancing security. In other words, better understanding what we were spending beyond just my office’s direct costs.”
Understanding Role Based Access Control (RBAC) via Idenhaus
This article serves as an introduction to understanding role-based access control and how it can benefit your organization.
Lawmakers introduce bipartisan bill for ‘internet of things’ security standards via The Hill
Under the bill, the National Institute of Standards and Technology (NIST) would create recommendations for the federal government’s use of internet of things devices, including establishing minimum security requirements to address the products’ cyber vulnerabilities.
UK code breakers drop Bombe, Enigma and Typex simulators onto the web for all to try via The Register
UK signals intelligence agency GCHQ, celebrating its centenary, has released emulators for famed World War II-era cipher machines that can be run within its web-based educational encryption app CyberChef.
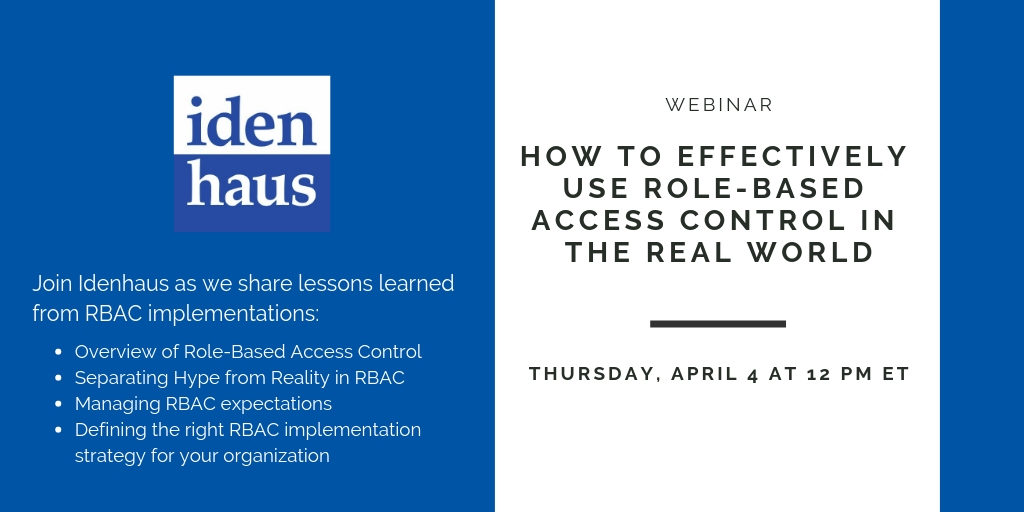
How to Effectively Use Role-Based Access Control in the Real World [WEBINAR] via Idenhaus
In this webinar, you will learn how to balance managing the complexity of RBAC and delivering value to the business effectively.
Check out our previous digest of Identity & Access Management articles here: 7 Must-Read IDaaS, Cybersecurity, and PAM Articles, February 2019
An IAM Assessment is a quick, expert evaluation of your environment that identifies and addresses the most common issues organizations face when implementing a solution.
This is ideal for organizations that:
- Are struggling to get their IAM solutions deployed
- Have a misalignment between their processes and technology
- Have an immature IAM solution with too many workarounds
- Companies that want to accelerate their IAM programs
Click here to learn more about the IAM Assessment.
Follow @Idenhaus on Twitter and subscribe to our biweekly newsletter.
By going to work quickly to solve the most challenging cybersecurity and identity management problems, Idenhaus takes the pain out of securing corporate information and assets for companies that aspire to maximize their potential in this digital age. Click here to contact us