Watch how easy it is for hackers to access personal information through social engineering. Today’s Identity Management and Cybersecurity digest includes articles covering ICS/SCADA, Identity Governance, Healthcare Cybersec, recent attack stats, and more.
Get this new digest delivered a day earlier by signing up for our newsletter.
Here are this week’s 8 must-read Identity Management and Cybersecurity articles.
Examining the cybersecurity landscape of utilities and control systems
The Bowman Avenue Dam incident illustrates a growing and disturbing reality: attackers are extending the threat from the online and virtual to the physical world, in which damage could be even more severe. Read more >>
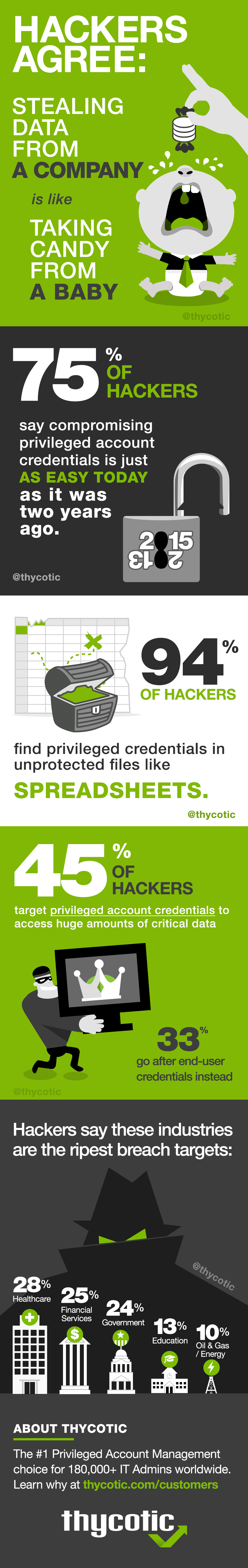
7 Need-To-Know Attack Stats
Facts & figures about average dwell times, incident response speeds, and which direction the ‘detection deficit’ is heading. Read more >>
Cybersecurity Efforts Require Individualized Planning and Execution
This article discusses the required elements of cybersecurity planning as they relate to a variety of typical private funds, including hedge funds and private equity funds. Read more >>
Why Do Some Identity Governance Strategies Fail?
Identity governance comes along after organizations have already begun implementing identity and access management (IAM) tools and processes. Because it comes later in the IAM project, you are forced to organize and establish a new order to a working environment. Read more >>
Have We Reached a New Era for Digital Identity Management?
Utah’s Chief Technology Officer David Fletcher says identity is not as simple as it might have been in the days before technology was infused in nearly every facet of daily life. The idea of multiple “identities” belonging to the same person has evolved as a very real concept in the online arena. Read more >>
The Stakeholders Have Spoken: NIST to Refine Cybersecurity Framework
The National Institute of Standards and Technology (NIST) is developing a minor update of its Cybersecurity Framework based on feedback from its users. In the just released Cybersecurity Framework Feedback: What We Heard and Next Steps, NIST is announcing that a draft of the update will be published for comment in early 2017. Read more >>
Breaking Down Barriers to Effective Information Security
A recent survey* was conducted by PricewaterhouseCoopers (PwC) and asked 9600 C-level leaders about obstacles to effective cybersecurity. Read more >>
Healthcare cybersecurity is reactive, must shift to ‘proactive threat hunting’ says Raytheon
Two-thirds of businesses, including organizations in the healthcare industry, wait until a cybersecurity attack before they engage a security vendor or a managed security services provider, according to a recent Ponemon study. Read more >>
If you enjoyed these articles, signup below to get the Idenhaus Identity Management & Cybersecurity News delivered to your inbox.
Photo Credit: Flickr