A three-part series examining the intricacies of integrating Role Based Access Control into a group environment.
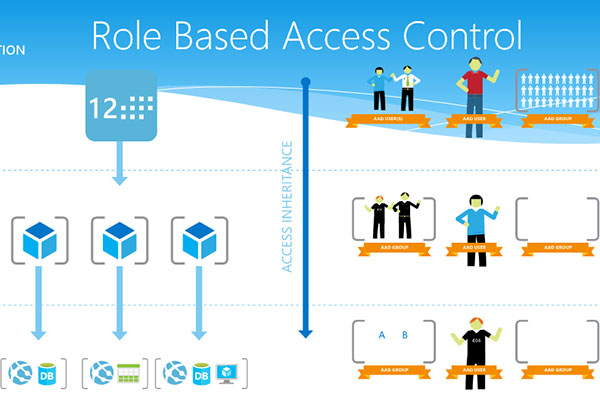
One of the biggest benefits of Role Based Access Control (RBAC) is that it provides a simple model to assign access rights to users based on their function or position. Further, the assignment of roles can be largely automated through an IAM solution, which reduces administration, improves security, and enforces policy in a consistent manner.
In Part I of this series, we discussed the importance of assessing the current IT environment, defining the business value of RBAC, and involving the proper business and technical stakeholders in the effort. In Part II we use the knowledge of the current state to gather requirements to build a Roles Catalog and define its structure. In this final post, I’ll outline the process to move forward and implement RBAC in your organization.
Part 3: Design, Develop, Deploy Your Roles
Continuing towards a successful Role Based Access Control integration into your security infrastructure, part three is where the rubber meets the road. Once the team is initiated and we have a collaborative environment, we can rely on greater chances of success as the architecture is designed, test plans are drawn, and the execution efforts begin.
Here are some solid recommendations to aid in the process:
1. DESIGN THE SOLUTION ARCHITECTURE
- Identify authoritative sources of identity and access control data
- Create a data map that shows available attributes from your Book of Record to your Identity Store and on to your Consumers (i.e. Applications and Systems)
- In place upgrade vs. add-on services
- Prioritize from Mission critical on down based on RBAC value add
- Does the role improve compliance and security? (e.g. Separation of Duties, Least Privileges)
- Are there a large number of users in a particular role?
- Is there a high volume of change (i.e., users moving into and out of a role)?
2. DEFINE THE TEST PLAN AND USE/TEST CASES
- Automate testing when/where possible
- Map enumerated requirements to use/test cases
- Plan for break/fix efforts
3. DESIGN AND DEVELOP
- Detailed attribute and data mapping cannot be underestimated
- Leverage iterative development and deployment lifecycles between Development and Test Environments
- Knowing the tools is as important as knowing how to develop
4. MAKE IT SO
- Deployment strategy
- Deploy to Administrative resources first
- Kick the tires and validate with a pilot group
- Plan for last minute adjustments
- Go-Live
- One small step or one giant leap? Shoot bullets before you shoot cannon balls
- Review, revise, and adjust
5. LESSONS WE’VE LEARNED INTEGRATING Role Based Access Control
- The foundation for design must be well-defined and flexible
- Avoid use of static value assignment to enhance flexibility
- Leverage existing tools and features vs. creating from scratch
- Keep the user interface simple
6. SOME SOUND ADVICE
- Know why you are implementing roles (e.g., business value), not just how
- Use the 80-20 rule and focus on a few key roles first
- Role Based Access Control Projects can be successful
- When in doubt, call in the professionals
We have presented a high-level framework to implement Role Based Access Control in a Group Environment that provides a common frame of reference for organizations. This supports the Idenhaus position that RBAC is both manageable and attainable, rather than an access control model that is great in theory, but not practical. Many organizations struggle with RBAC. To realize its promise, a disciplined, methodical approach is key to successful deployment.
Read Part 1 and Part 2 of this series. For further reading on RBAC, check out these resources:
- Part 1: Defining Roles for IAM – Begin at the Top!
- Part 2: Defining Roles for IAM – From the Bottom Up
Click here to subscribe to the blog
Follow @Idenhaus and connect with Hanno on LinkedIn.
By going to work quickly to solve the most challenging cybersecurity and identity management problems, Idenhaus takes the pain out of securing corporate information and assets for companies that aspire to maximize their potential in this digital age. Click here to contact us






