A three-part series examining the intricacies of integrating Role Based Access Control into a group environment.
In part one of this series on integrating Role Based Access Control (RBAC), we provided a high-level overview of the necessary footwork to prepare stakeholders for the organization-wide change that comes with the territory. In this second part, we will do a deeper dive into the process of the requirements gathering that is necessary before embarking on building a catalog of roles and its structure. Other aspects to consider are best practices in managing access requests, integrating roles from various sources, and ongoing management of the Groups, Users, Roles, and Privileges.
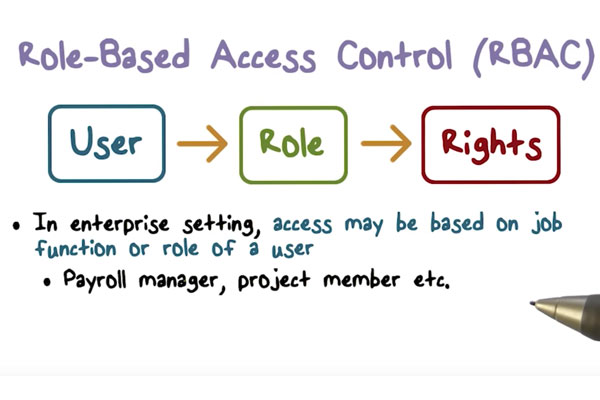
For review, RBAC is a methodical approach to provisioning based upon roles and privileges in contrast to a rule-based or discretionary approach. Roles simplify access management for employees, contractors, and external users by incorporating the business policies and rules necessary to grant appropriate access.
Part 2: Requirements Collection, Prioritization, and Cataloging
In order to successfully integrate RBAC into your security infrastructure, it is imperative to facilitate a collaborative environment in which to gather information. These detail-oriented exercises will help you lay a solid foundation, pay dividends when defining scope and priority, and assist with gaining the essential stakeholder buy-in and approval.
Based on our experience integrating RBAC, we’ve put together 9 steps and recommendations to aid in the Collection, Prioritization, and Cataloging process of an RBAC integration.
1. GET READY AND GATHER REQUIREMENTS
- Facilitated Sessions
- Business Process Mapping
- Leverage Lean or other business process optimization tools
- Identify other active projects that may be impacted or impact this project
- Capture and communicate working session workflows and requirements
2. ROLE CATALOGUE STRUCTURE AND ITS DESIGN
- Administrative Roles
- Operational Roles
- Approval Roles
- Escalation Process
- Permission Roles
- Security Clearance Roles
- Resource Permission Roles
- Inheritance of Permissions
- Separation of Duty Policies
3. GET STAKEHOLDER BUY-IN ON ROLE CATALOGUE STRUCTURE
Your stakeholders have skin in the game, and they stand to benefit or suffer depending on the outcomes. There cannot be enough emphasis put on how important it is that they participate in the definitions process.
4. MANAGING ROLE REQUESTS WITH WORKFLOWS
-
- Workflows for requesting and approving assignment of roles
- Defining the escalation procedures
- Define the notification requirements
5. INTEGRATING ROLES WITH CONNECTORS
- Determine which Roles will be created manually and which will be dynamically built based on system events
- Identify the trigger events for creating dynamically generated roles
6. DEVELOP A STRATEGY FOR MANAGING ROLES, USERS, GROUPS, AND CONTAINER PRIVILEGES
- Roles must be managed
- Define Trustee Rights for each role category
7. PREPARE THE RBAC PROJECT SCOPE AND PRIORITIZATION MATRIX
- Leverage tools to help prioritize requirements
- Classify requirements into deliverable work items
- Requirements Prioritization Survey
- Requirements Facilitated Session
- Prepare a scoping and prioritization matrix
- Obtain stakeholder approval of scoping and prioritization matrix
8. KNOW WHAT TO EXPECT DURING AN RBAC INTEGRATION
- Stay focused on the business processes and manage the political issues
- Plan on performing 2-3 requirements reviews
- Logically enumerate requirements
- Know the resource limitations and adjust efforts within scope accordingly
- “That’s not the way we do it here” – contingency planning.
9. IMPORTANT LESSONS WE’VE LEARNED INTEGRATING RBAC
- Properly defined requirements and scope lead to a more successful project, take the time to get them right.
- Build consensus on the project objectives and the political issues sometimes resolve themselves.
Before you begin the Collection, Prioritization, and Cataloging process, it’s imperative to first conduct a needs analysis, evaluate the current access landscape, and preparing stakeholders for the organization-wide change that comes with a role based access control integration. Click here to read Part 1: How to Successfully Introduce Role Based Access Control into a Group Environment.
Stay tuned for our final installment on RBAC. Learn more about how to get started with Role Based Access Controls, check out these resources:
- Part 1: Defining Roles for IAM – Begin at the Top!
- Part 2: Defining Roles for IAM – From the Bottom Up
Click here to subscribe to the blog
Follow @Idenhaus and connect with Hanno on LinkedIn.
By going to work quickly to solve the most challenging cybersecurity and identity management problems, Idenhaus takes the pain out of securing corporate information and assets for companies that aspire to maximize their potential in this digital age. Click here to contact us






