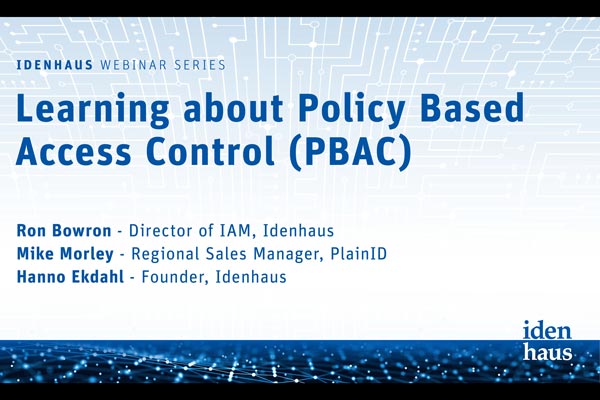
9 Identity Management Articles for Cybersecurity Professionals
IAM, APTs, and Self-Sovereign Identity headline this week’s digest of Identity Management articles for Cybersecurity Professionals. Thanks for checking out this week’s digest of articles for Cybersecurity Professionals. Click here to view the healthcare-focused digest. Peruse our resources for webinars, case studies, infographics, and educational videos. Subscribe to our Identity Management biweekly and/or our Healthcare Cybersecurity and IAM digest, delivered Tuesdays at […]
9 Identity Management Articles for Cybersecurity Professionals Read More »