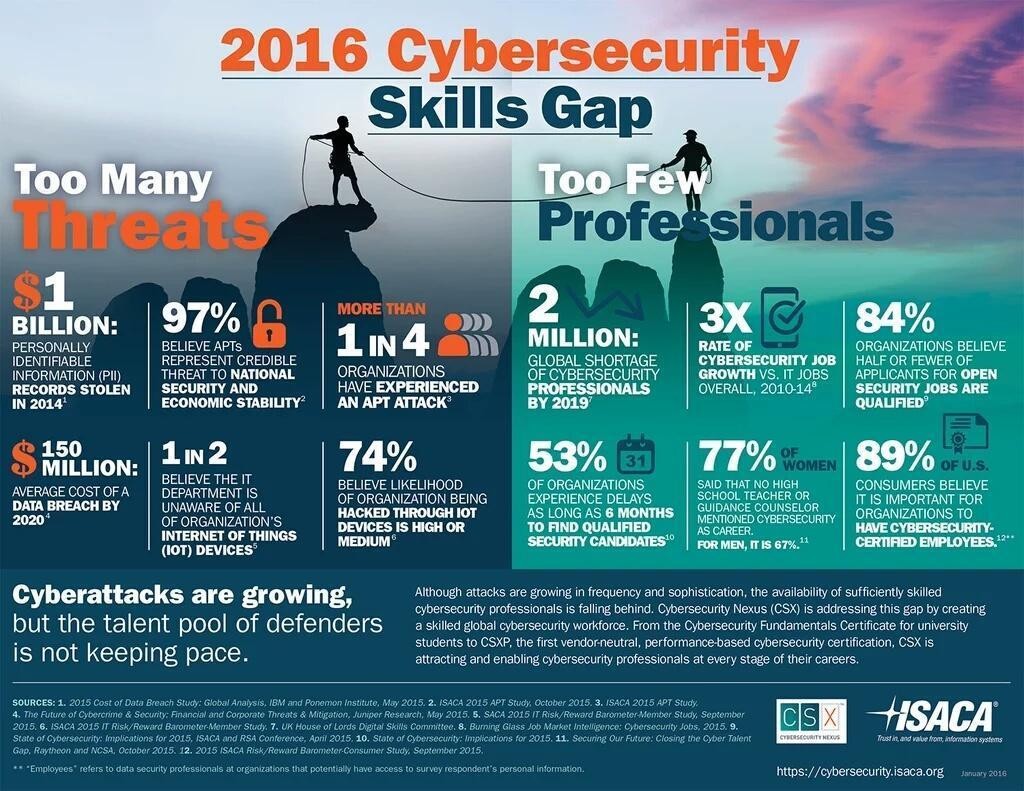
Why Defense-in-Depth Is Critical to Cybersecurity Strategy
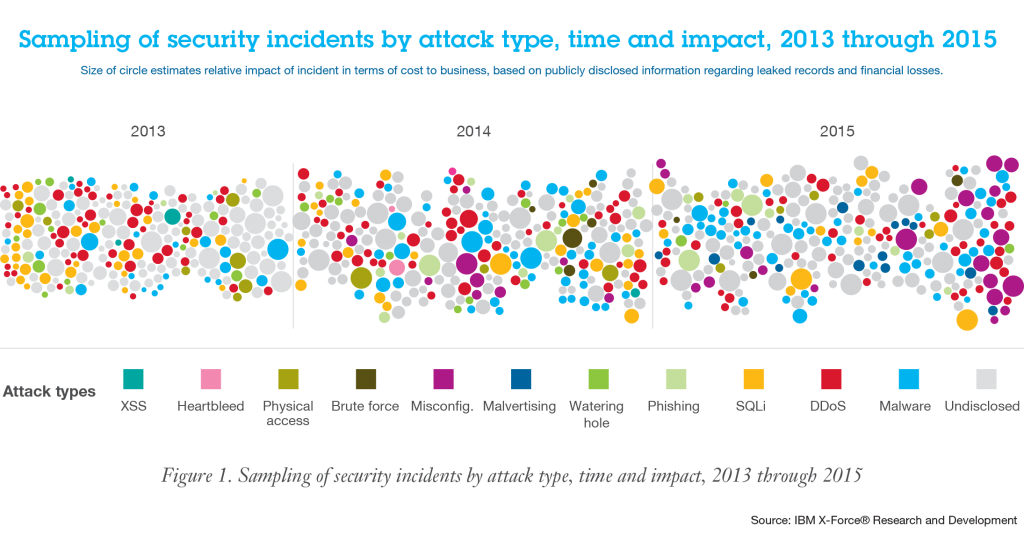
Since the inception of Cybersecurity twenty-plus years ago, the industry has gone through a plethora of iterations. The Internet was initially designed to be an open environment to enable information sharing between academics and researchers. When businesses and government agencies joined the network explosion in the late 1990s, the open environment turned into a security […]
Why Defense-in-Depth Is Critical to Cybersecurity Strategy Read More »