Part 1: Defining Roles for IAM – Begin at the Top!
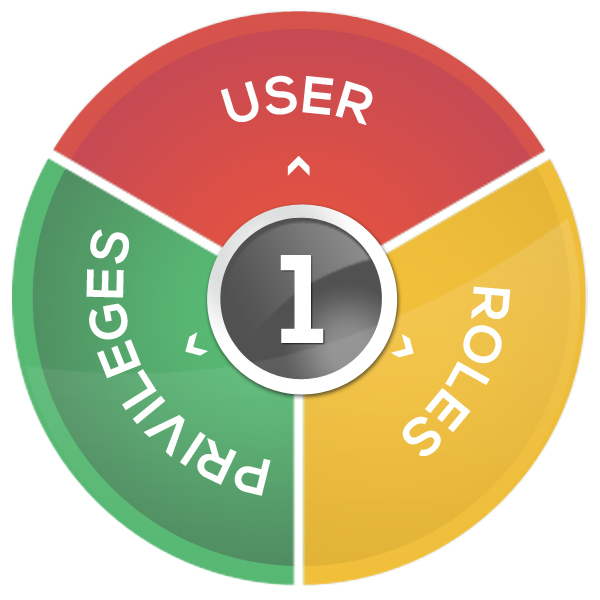
Implementing roles-based access control is invaluable, when implemented correctly. Roles simplify access management for employees, contractors, and external users by incorporating the business policies and rules necessary to grant appropriate access; allowing the Identity Management solution to grant, modify and revoke access automatically. Just as importantly, roles simplify compliance as well, making it easier to […]
Part 1: Defining Roles for IAM – Begin at the Top! Read More »