
Imagine the challenges large enterprises face onboarding and off-boarding thousands of users, properly managing their access, consistently applying security policies, and complying with a sea of regulations. Challenges like these can be addressed and overcome with a robust Identity Management solution. However, that’s much easier said than done. Comparing the strengths and promises of one solution compared to another can be overwhelming and confusing. Organizations often discover that all IAM vendors have one or two standout features, but few are good across the board.
The proliferation of vendors and the wide range of offerings to consider tempt leaders to short-change the evaluation process and focus on one or two key features. As such, many organizations deploy Identity & Access Management (IAM) solutions based on surprisingly vague, simplistic, and unrealistic business cases that do not do justice to the multi-million dollar investments they require. The resulting lack of alignment between IT and business further jeopardizes the creation of value and eliminates the hope of any return on investment. Moreover, a roadmap that lays out a plan to implement the IAM solution and deliver value to the business is usually an afterthought, if it is given any consideration at all.
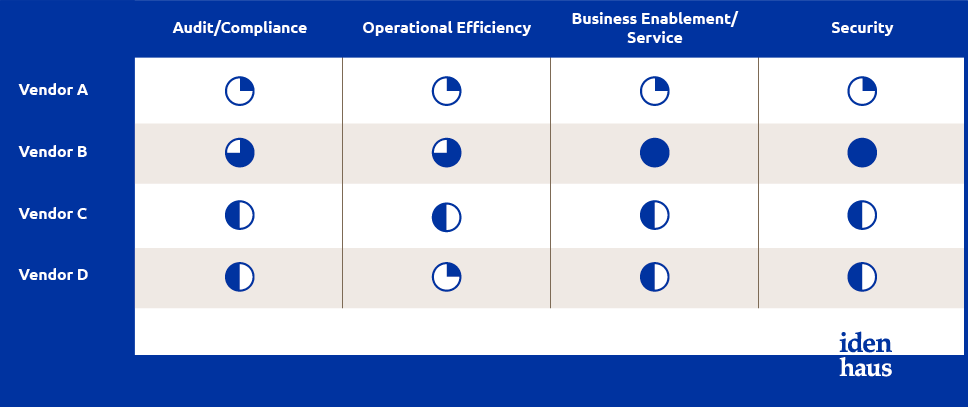
Based on combined learning from clients, case studies, and research, we recently identified the four key IAM business drivers:
- Audit/compliance
- Operational efficiency
- Business enablement/service
- Security
To successfully drive product selection and deliver the full value of an Identity Management solution, we recommend developing a decision framework, or scorecard, that combines investments in people and IT capabilities.
Here are the key elements that should be considered for each business driver on the Scorecard:
1. Compliance
- Reporting capabilities (Out of the box)
- Ability to customize reports
- Detailed logging capabilities
- Ability to correlate data
- Integration with SIEM tools
2. Operational efficiency
- Scalability
- Authentications
- Account provisioning
- Assess existing in-house IT Skills; Evaluate options for staff training on technology
- Define metrics/Key Performance Indicators
- Ability to automate routine operational tasks (e.g. connectors to key apps/systems; maturity of connectors)
- Supports approval workflows
- Stability of environment
- Clear error messages
- Ability to re-send transactions for processing
3. Business enablement/service
- Password self-service
- Self-service requests for software
- Workflows to request access
- Administrative portals (e.g. manage group memberships)
4. Security
- Mature policy engine
- Centralized password policies
- Ability to customize compliance
- Governance
- Segregation of Duties
- Least privileges
- Ability to assign thresholds for notifications/response when policy is violated
The scorecard method provides a framework that decision-makers can use to stay focused on the most important features and benefits while evaluating IAM Solutions.
We further recommend identifying non-negotiable “must-haves” under each business driver and prioritizing those features. Not only will this improve the odds of finding the right solution, but these “must-haves” will keep you from getting distracted by bright-shiny objects and promises that aren’t important to your organization. Most importantly, be sure to budget for the time and expense of switching solutions and expect some disruption to normal business processes.
Read part 1 – Common Business Drivers for Adopting Identity Management Solutions.
Follow @Idenhaus on Twitter and subscribe to our biweekly newsletter.
Photo credit: Mark Lord Photography
Learn more about the top challenges that companies face when implementing Identity & Access Management and how to overcome them in our new book:
Grab it for free here: Click to download!
By going to work quickly to solve the most challenging cybersecurity and identity management problems, Idenhaus takes the pain out of securing corporate information and assets for companies that aspire to maximize their potential in this digital age. Contact us






