
Technology is a third rail because the implementation of technology is by far the easiest thing to mess up for any organization and no one wants to talk about it.
This is the last installment of the four-part “What is Cybersecurity?” series. While no ground-breaking truths have been uncovered, we’ve presented information that is necessary for leadership and management to start understanding that cybersecurity is not a “one-size fits all” environment. Each organization has a unique network–that’s hopefully only as big as is required–coupled with a unique mission. Security requirements are also unique because different organizations require different security measures.
Yet, there is still an 800-lb gorilla sitting in the corner.
What’s worse, there is a large elephant in the room as well.
And that elephant is pink.
Technology, technology, technology.
It is what makes the world go round for cybersecurity professionals. Without it, there wouldn’t be any cybersecurity professionals. Still the issue remains: what is useful technology for an organization to be effective, without breaking the piggy bank?
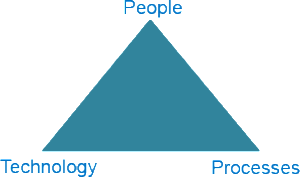 In the first two posts we discussed how people and process are two overlooked facets of the cybersecurity environment. We looked at how people can sometimes be overlooked and process negated because we are dealing with computers. Yet, without those two facets the cybersecurity triangle would fall apart and not function effectively.
In the first two posts we discussed how people and process are two overlooked facets of the cybersecurity environment. We looked at how people can sometimes be overlooked and process negated because we are dealing with computers. Yet, without those two facets the cybersecurity triangle would fall apart and not function effectively.
This post represents the final side of the triangle, or as I like to think, the cybersecurity “third rail”: technology.
The Third Rail
As those of you who have read my previous posts know, I like to point out when I am presenting obvious information. I feel this is necessary for you to understand I’m not making some grand discovery in how the cybersecurity profession views things. Another obvious point is that technology is a requirement to play in the cybersecurity pool. Computers process information faster than humans. (Captain Obvious strikes again.) Computers work fast and, in order to protect your network from computers, you need to use computers. Cybersecurity is one of the areas where a most people will understand humans cannot keep up with computers. This is why we must have technology as our third side of the triangle.
If everyone knows this, why is it a third rail?
Technology is a third rail because the implementation of technology is by far the easiest thing to mess up for any organization and no one wants to talk about it. To be fair, no one is a harsh generalization, but it gets the point across. The simple fact is that technology is oversold and its importance is overvalued.
Now I’m confused. If I need technology and it is required to play in the pool, then how can it be oversold and overvalued?
Cybersecurity technology is oversold and overvalued because the methodologies the technology employs are often sold as being everything the organization needs to protect its networks. In today’s cybersecurity landscape, cybersecurity professionals with experience and understanding of the issues at hand are hard to find. Rightfully so, as large organizations grab them up as quickly as possible to protect their networks. The remaining organizations with smaller pockets usually turn to their IT department or hire a less experienced cybersecurity professional who may believe the hype being sold by the technology companies. I’m not against the hype. Sales are sales, but it does come to a point where organizations need to be able to understand and select technologies which are right for them.
I’m still not clear why it is a third rail? Isn’t that something you don’t want to talk about?
Cybersecurity technology is a third rail because the truth is not always convenient for everyone to hear.
Billions of dollars, maybe trillions, has been spent in the research, development, and deployment of cybersecurity technology. The industry has grown so large that it can be daunting for the uninitiated to even grasp the minute differences between the offerings. Truth be told, it can be daunting for experienced professionals not to get caught up in the craziness and prefer one solution over another. This is not a bad thing, but can be detrimental if the solution they love isn’t the best fit.
The ugly truth no one wants to talk about is that you don’t need three or four different pieces of technology to properly defend your network. Chances are you only need one or two, combined with the right people and processes, to properly protect your information.
Building the Right Toolbox: What Technology Do I Need?
That is the million (or billion) dollar question. Technology is definitely not a one-size fits all solution and it may not even be necessary depending on your network environment. A network environment is defined (by me) to include the size and setup of your network, as well as the way you use your network. These are the two underlying factors when determining the type of technology you should consider.
If it is that easy, then why do I need cybersecurity professionals?
The reason you need cybersecurity professionals (and, yes, I understand this may seem self-serving) is to have dedicated individuals who are only focused on securing the network.
As discussed in my previous posts, when you overload individuals, security becomes their second or third priority. Then, the precedent is set for security to come second or third to the rest of the organization’s network operations.
There is really only one rule for technology: Don’t overdo it.
There, I said it.
Not every organization needs to have one of everything and not every organization only needs one thing. This is the hard part about cybersecurity: understanding what you need and what you can afford. As we discussed earlier, not every network is in the same situation.
Here are three questions to consider when you are looking at cybersecurity technology:
- What am I trying to achieve by implementing this technology?
- What do I need to protect?
- What type of network activity do I want?
Those are just the basics, but it will get you started.
Any cybersecurity professional can make your network secure; it’s called “don’t connect to the Internet.” That is not a realistic option. As such, every network is operating under a certain level of risk to compromise. All any organization can do is mitigate the risks and identify potential issues to maintain a constant vigil for those areas of potential compromise.
Check out Part 1, Part 2, and Part 3 of the series.
Subscribe here to get the top IDM & Cybersecurity articles delivered to your inbox twice a month. Follow us @Idenhaus or connect with us on LinkedIn.
Photo credit: Perspecsys






