Stay informed with our biweekly Identity Management & Cybersecurity news digest. We curate the best IAM & Cyber security articles to help you navigate the ever-changing IT landscape. Subscribe to our biweekly newsletter here.
Here are 5 informative and insightful IAM and cybersecurity articles from September 2018. Enjoy!
How Identity Management Makes GDPR Compliance Easier via Idenhaus
The ability to properly control privacy data is becoming a minimum requirement for organizations to operate, public and private alike. Not only are there large financial penalties at stake, but there is also the risk of reputation loss.
Modern Authentication Methods and How They Enhance User Security via TechTarget
A set of symbols is no longer a reliable way of securing personal data, and this has pushed companies to work on more advanced security methods.
How identity layering improves data flow via CSO
Having a layered approach to designing an identity ecosystem does not mean you cannot have key components like a “data store”. However, it allows you the freedom to think of these components in a more creative way.
Browser Extensions: Are They Worth the Risk? via Krebs On Security
If you’re the type of person who uses multiple extensions, it may be wise to adopt a risk-based approach going forward.
Successfully Integrating HR Processes with Identity Management [WEBINAR] via Idenhaus
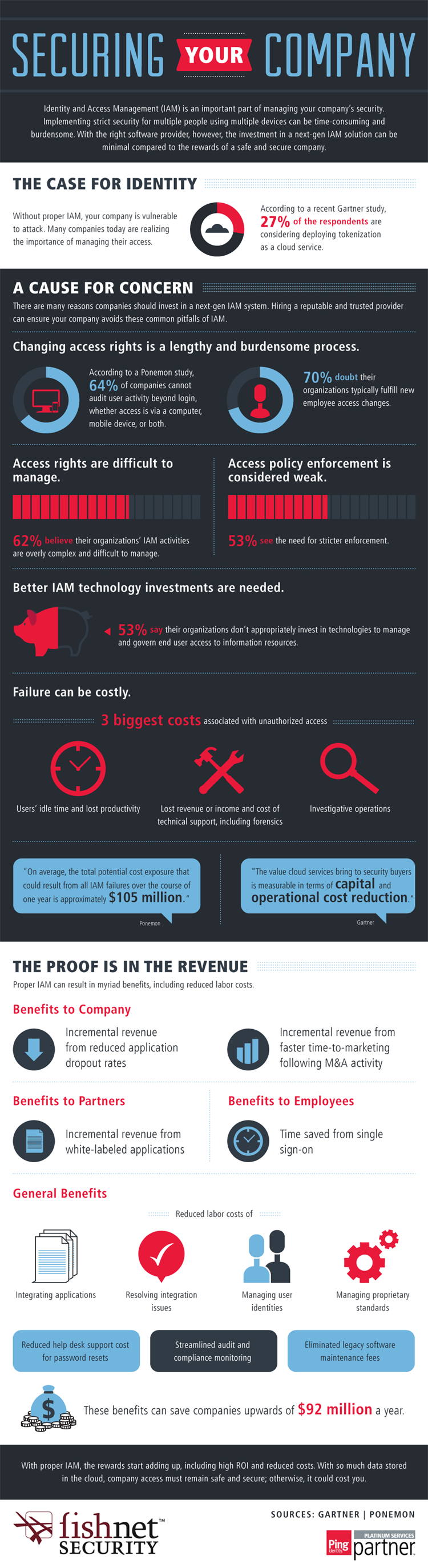
Unlike other areas of security, IAM focuses on provisioning and managing user permissions across a broad range of applications across the enterprise, which makes a successful IAM implementation profoundly impactful.
Download my new, FREE digital book entitled Reimagining Identity Management: How To Design, Choose And Implement The Right IAM Solution For Your Business.
Follow @Idenhaus on Twitter and subscribe to our biweekly newsletter.
By going to work quickly to solve the most challenging cybersecurity and identity management problems, Idenhaus takes the pain out of securing corporate information and assets for companies that aspire to maximize their potential in this digital age. Click here to contact us