In 2016, President Obama established the Commission on Enhancing National Cybersecurity, which was created to “…[recommend] bold, actionable steps that the government, private sector, and the nation as a whole can take to bolster cybersecurity in today’s digital world.” The Commission recently published their recommendations in its “Report on Securing and Growing the Digital Economy”. The scope of the report is government-centric, although the Commission did highlight the need for better public-private relationships; a recommendation that was on point. While many of the findings are not particularly novel, there were some interesting ideas in the report which are summarized below.
1. Public/Private Partnerships are Essential
One of the strongest themes in the report was the need for collaboration between the private sector and government, beginning with the development of a cybersecurity roadmap to enhance the security and resilience of our digital networks. Moreover, the Commission proposed a new model for defending and securing the convergence of the cyber and physical by creating a public/private initiative to promote the adoption of strong authentication to improve identity management. The increasingly complex nature of cybersecurity challenges, along with Nation-State funded attacks, are creating incentives (and the imperative) for government and business to collaborate more frequently and in new ways. Ultimately, better cooperation between the public and private sectors will drive the cybersecurity solutions of the future.
2. Cybersecurity for Small Businesses
Often overlooked, Small Businesses were front and center in Recommendation 1.5, which focused on how to provide better security guidelines for small businesses, and defined methods to better inform small companies about cybersecurity risks based on known intrusion incidents. While the recommendations are solid, they fail to address the fundamental issue which is the lack of personnel and financial resources Small Businesses have to dedicate to these issues.
In the end, it will probably be the State and Local governments that get more involved; driving the development of mature, local cybersecurity programs. Faced with limited resources and a growing set of security responsibilities, Small Businesses will need to leverage every available resource to address cyber-crime and day-to-day cybersecurity activities. Developing new community resources to share knowledge and skills offers a cost-effective ‘force multiplier’ to drive benefits at the local and state levels. State and local governments will have to provide more resources, either through a state-sponsored program or through cybersecurity professional chapters in the local community.
3. Cybersecurity Product Labels
The Commission has made a recommendation to implement a cybersecurity labeling system for IoT devices. IoT devices are defined by the commission as any networkable technology, sold for either commercial/industrial or personal use. The basis of this cybersecurity label would be modeled after Underwriter Laboratories (UL), which tests and certifies products for the consumer. This problem of testing and certification works well for products, but it is a challenge in cybersecurity.
One of the basic tenants of cybersecurity is understanding your vulnerabilities. In establishing the cybersecurity label, a case could be made the liability for any vulnerabilities not previously identified could lie with the underwriting association conducting the evaluation. One of the ways to address this would be to only have the cybersecurity label once secure programming practices are ingrained as the standard, but secure software will be a challenge to implement due to the speed and transparency of most software.
Instituting a cybersecurity label is a good way forward, but it is a long-term option, which will take time to understand the requirements for the label and then the general acceptance of the public in wanting the label on the products. The Commission is not blind to the fact a large education campaign will be required to inform the public of the benefits of this label. I would also state a large education campaign will need to be conducted within tech companies to ensure they understand the breadth and scope of this requirement.
4. Centralizing Cybersecurity
The last topic in this post is the Commission’s recommendation to centralize the US Government’s networks and cybersecurity to better share components and best practices, which is a great idea. This recommendation eliminates the need for each agency manage its own IT infrastructure as is mostly the case today. The best part of this proposal is that any cybersecurity issues will be managed through a centralized cybersecurity agency, a one-stop shop for the entire United States.
In the current cybersecurity operations model, each Department or Agency has cybersecurity recommendations for their sectors. This distributed, agency-centric model was developed piecemeal in response to either Congressional mandates or an Executive Order. That is, the model was accidental (reactive) rather than planned (proactive). The resulting decentralized structure has led to issues in identifying stakeholders, researching incidents, and providing effective cybersecurity programs; a centralized cybersecurity organization will help to clarify those issues.
As a final thought, a centralized organization also makes response coordination and information sharing easier between the Federal, State, and Local governments by eliminating unnecessary bureaucracy and giving cybersecurity operations a more prominent position.
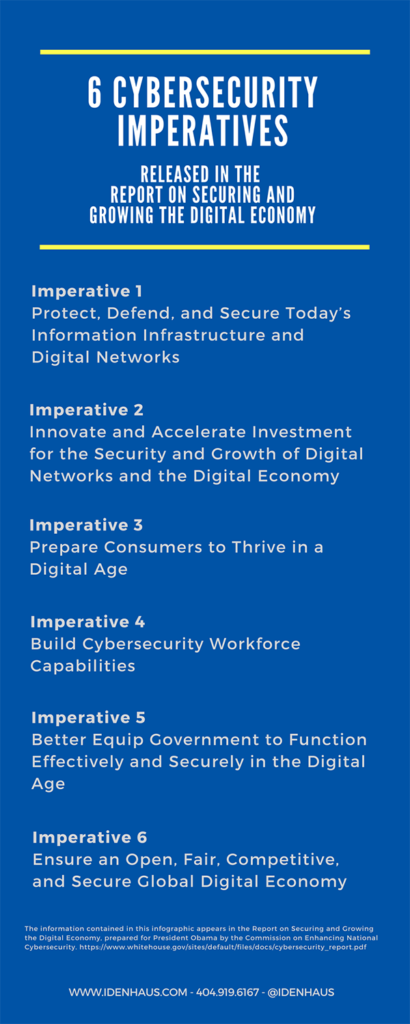
Six Cybersecurity Imperatives
The Commission had a tough task to develop this report with a broad scope, on a complex topic, in a short timeframe. Nonetheless, this document provides a solid foundation for taking the nation’s cybersecurity capabilities to the next level. There are many concrete recommendations that should be considered, prioritized and implemented to bolster the United States’ cybersecurity program. Along those lines, there were 6 Cybersecurity Imperatives that the Commission established. They are:
You can read the full report here.
Click here to subscribe to our blog and follow @Idenhaus on Twitter.
By going to work quickly to solve the most challenging cybersecurity and identity management problems, Idenhaus takes the pain out of securing corporate information and assets for companies that aspire to maximize their potential in this digital age. Click here to contact us today!






