
Stakeholder engagement is arguably the most important component of a successful Identity Management project. Yet organizations often treat stakeholders as an afterthought or a fringe activity that is secondary to their technical implementation.
Successful IAM projects rely on the input from a range of stakeholders to identify requirements and integrate processes and data to drive the desired outcomes. People will only provide this valuable input if they are engaged. The phrase “stakeholder management” implies that these people can be made to respond positively to a project, but the truth is that IAM project teams frequently have no formal power or authority and therefore have to rely on influence to drive engagement to achieve their objectives.
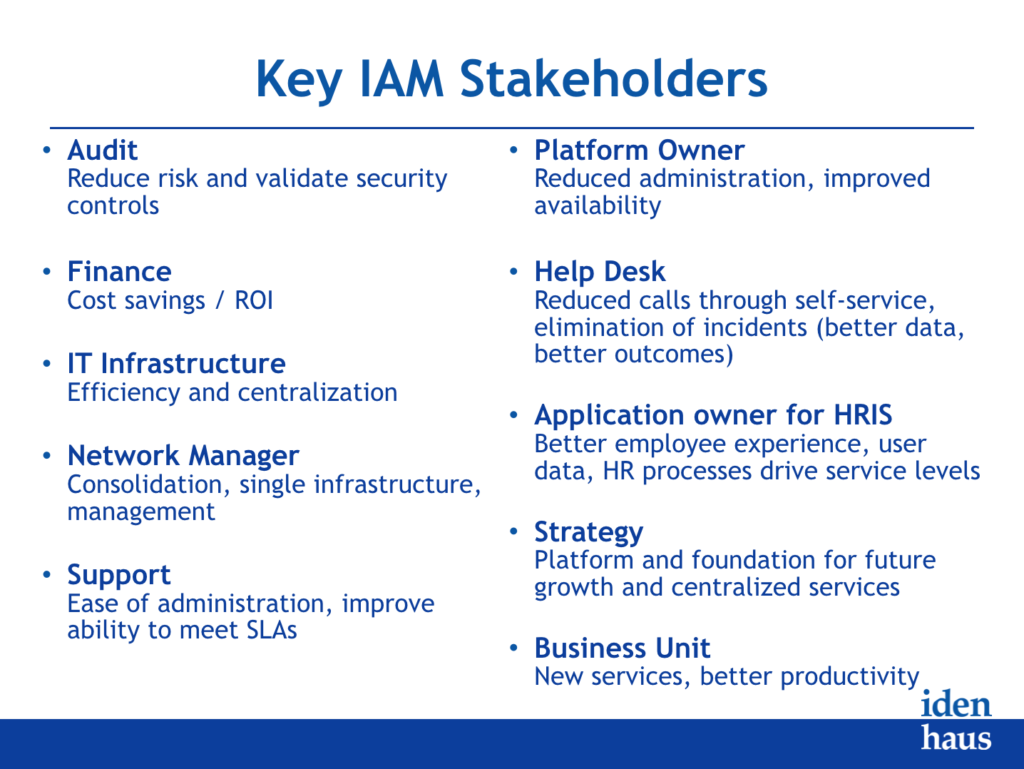
Idenhaus recommends conducting a kick-off meeting to engage stakeholders from the outset, and then conduct a series of interviews and workshops to capture stakeholder input. Here are the most common IAM stakeholders that every organization should engage early and often.
- Audit
- Finance
- IT Infrastructure
- Network Manager
- Support
- Platform Owner
- Help Desk
- Application Owner for HRIS
- Strategy
- Business Unit
Engagement focused on controlling stakeholders and managing risk is valuable, but not sufficient to achieve excellence in solution design. Engagement that is oriented to collaborating with stakeholders can lead to learning, innovation, and fundamental corporate transformation.
Our IAM methodology incorporates practical steps that corporate leaders can employ to put a collaborative approach in place. In our experience, engaging stakeholders builds social capital that provides more access to information, improved influence, and the benefit of support rather than scrutiny should unexpected problems arise.
Learn more about how to design, choose, and implement the right IAM solution for your business in our digital book Reimagining Identity Management in the Digital World. Click here for a free copy.
Follow @Idenhaus on Twitter and subscribe to our biweekly newsletter.
Photo credit: Flickr
By going to work quickly to solve the most challenging cybersecurity and identity management problems, Idenhaus takes the pain out of securing corporate information and assets for companies that aspire to maximize their potential in this digital age. Click here to contact us






